Aaliyah Nicole C. Oriente
—— Cybersecurity Analyst

About Me, Myself & I
I am Aaliyah Nicole C. Oriente, an 18-year-old aspiring Cybersecurity Analyst. I am committed to broadening my understanding of advanced web technologies and developing a strong technical foundation. I demonstrate cooperation, dependability, determination, adaptability, and versatility, which support my effectiveness in diverse environments. My goal is to continually enhance my competencies and contribute to innovative and meaningful digital advancements.

Personal Information
Name: Aaliyah Nicole C. Oriente
Age: 18 years old
Date of Birth: August 17, 2007
Gender: Female
Address: Prk. Maguindanao, Lun Padidu Malapatan Sarangani Province
Religion: Roman Catholic
Blood Type: O
Civil Status: Single
Citizenship:
Height: 152.4 cm
Weight: 34kg
Contact: 09051182146

Hobbies/Interest
- Playing Instruments
- Reading Books / Sleeping
- Listening Music / Eating
- Editing / Making Digital arts
- Board Games / Puzzle Games
- Traveling

Skills
- Time Management
- Critical Thinking / Problem-Solving
- Adaptability
- Communication
- Programming
“Analyzing risk, Amplifying security.”
Your First Line of Defense in the Digital World.
I’m Aaliyah Nicole C. Oriente, a dedicated Cybersecurity Analyst with a strong interest in threat detection, vulnerability assessment, and secure system practices.
I enjoy working in fast-paced environments where I can analyze risks, strengthen defenses, and contribute to building safer digital infrastructures.
With a detail-oriented mindset and a commitment to continuous learning, I aim to support organizations in staying resilient against evolving cyber threats.

Biography: Building Secure Futures in the Digital Age
An aspiring IT professional known for her strong analytical mindset and passion for building secure, efficient, and user-friendly technological solutions. With a growing background in hardware troubleshooting, software management, and cybersecurity fundamentals, she has developed a solid foundation in identifying system issues, implementing effective solutions, and supporting reliable IT operations.
Driven by curiosity and a commitment to continuous learning, Aaliyah actively explores emerging technologies, strengthens her technical skills, and embraces new challenges in the field. She is particularly interested in cybersecurity, network administration, and IT support—areas where she excels in problem-solving, attention to detail, and clear communication.
Whether assisting end-users, analyzing system vulnerabilities, or maintaining IT assets, Aaliyah brings a proactive attitude and a strong sense of responsibility to every task. Her goal is to grow as a skilled IT specialist who helps organizations stay secure, productive, and technologically adaptive in an ever-evolving digital world.


My Chosen Field and Why I Specialize in It
I chose to specialize in Information Technology, with a particular focus on Cybersecurity Analyst, because I am deeply interested in how systems work, how data flows, and how digital environments can be protected against evolving threats. Technology is constantly advancing, and with that growth comes the need for reliable security—something I am passionate about providing.
I specialize in this field because I enjoy solving complex problems, analyzing vulnerabilities, and ensuring that systems remain safe, stable, and efficient. Cybersecurity allows me to combine critical thinking with technical skill, and it gives me the opportunity to make a meaningful impact by protecting people, organizations, and information from potential risks.
Most importantly, I am driven by the challenge of staying ahead of emerging threats and the responsibility of helping build a safer digital future.
SKILLS
Security Operations (SecOps): Threat Triage, Incident Response, Log Analysis, Security Monitoring, Alert Tuning.
Threat Intelligence & Hunting: MITRE ATT&CK Framework, Behavioral Analysis, Indicator of Compromise (IoC) Identification.
Cloud Security: AWS/Azure Security, IAM Policy Management, Infrastructure-as-Code (IaC) Scanning.
Vulnerability Management: Scanning, Prioritization, Remediation Planning, Configuration Auditing (CIS Benchmarks).
Scripting & Automation: Python (for task automation), Bash/PowerShell.
TOOLS
SIEM/Logging: Splunk, ELK Stack (Elasticsearch, Logstash, Kibana), Sentinel.
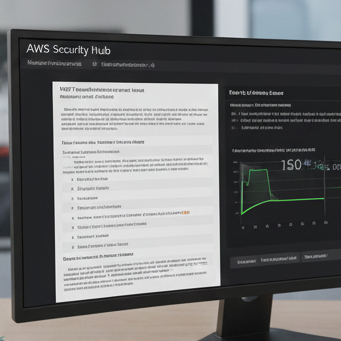
Cloud Platforms: AWS Security Hub, Azure Security Center, Prowler, ScoutSuite.
Scripting/Code: Python, VS Code, Git/GitHub.
Operating Systems: Linux (Kali, Ubuntu), Windows Server.
Network Analysis: Wireshark, tcpdump.
CERTIFICATES
CompTIA Security+: Validates foundational knowledge of core security functions.
(ISC)² Certified Cloud Security Professional (CCSP): Demonstrates expertise in securing cloud environments and services.
Splunk Certified User: Proficiency in searching, analyzing, and visualizing data within the Splunk platform.
Certified Ethical Hacker (CEH): Shows understanding of attack vectors and defensive countermeasures from a penetration testing perspective.
GIAC Certified Incident Handler (GCIH): Focuses on incident handling and forensic analysis for a rapid and effective response to security breaches.
Projects
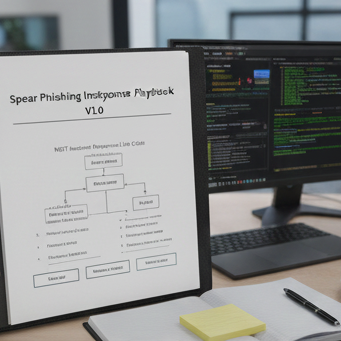
Spear Phishing Incident Response Playbook Development
I created a standardized Spear Phishing Incident Response Playbook tailored for the organization’s high-value targets (executives and finance). The playbook outlines clear, step-by-step procedures for the SOC team, including initial containment, eradication steps using EDR tools, and communication protocols.
It incorporates a checklist based on the NIST Incident Response Life Cycle to ensure no critical steps are missed during high-stress scenarios. This document serves as the primary guidance for rapidly mitigating sophisticated, targeted email attacks.
Customized Security Awareness Training Module
This project involved developing a custom, gamified security awareness module focused specifically on Insider Threat scenarios, a weakness identified in previous audits. I created three interactive, scenario-based quizzes addressing sensitive data handling, clean desk policy, and password sharing risks.
Post-module metrics showed a 25% improvement in simulated reporting compliance for PII (Personally Identifiable Information) breaches among pilot users. This initiative demonstrates an ability to translate complex security concepts into accessible, actionable training for non-technical staff.
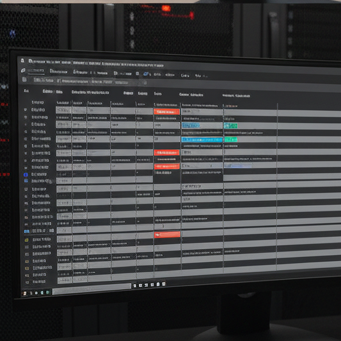
Hardening of Network Perimeter Firewalls
I performed a comprehensive audit and optimization of firewall rule sets on the simulated network perimeter (Cisco ASA). The primary goal was to implement the principle of least functionality by decommissioning over 150 legacy and redundant access control list (ACL) entries.
By documenting and rationalizing all remaining rules, I reduced the firewall’s processing load and decreased the overall complexity of the policy management. This proactive measure significantly improved the security posture by minimizing the chance of an unintended open port being exploited.
Blog/Article Section
The Cybersecurity Arms Race: Preparing for the Quantum and AI Era
The future of cybersecurity will be defined by an escalating arms race driven by two monumental technologies: Artificial Intelligence (AI) and Quantum Computing. Attackers are already leveraging generative AI to automate highly convincing deepfake social engineering attacks and create sophisticated, polymorphic malware at scale. This lowers the barrier to entry for cybercrime and demands an immediate shift in defense strategy.
In response, analysts like Aaliyah Nicole C. Oriente must evolve from reactive triage to proactive, AI-powered defense. Machine learning models are becoming indispensable for real-time anomaly detection, allowing SecOps teams to identify and neutralize threats in minutes, not hours.
Looking further ahead, Quantum Computing presents a foundational threat. Once powerful quantum machines are developed, they will be capable of breaking the asymmetric encryption (like RSA) that secures nearly all global data—from banking transactions to critical infrastructure communications. This existential threat requires the urgent adoption of Post-Quantum Cryptography (PQC). The cybersecurity professional of tomorrow must be prepared to manage this complex transition, shifting the industry focus toward Zero Trust Architecture and robust, quantum-safe protocols to ensure our digital world remains secure.